Politician Impersonations - Scammers Weaponizing Political Passion
 The landscape of digital fraud has shifted away from generic phishing emails and obvious scams into something far more industrialized and deeply personal.
The landscape of digital fraud has shifted away from generic phishing emails and obvious scams into something far more industrialized and deeply personal.
 The landscape of digital fraud has shifted away from generic phishing emails and obvious scams into something far more industrialized and deeply personal.
The landscape of digital fraud has shifted away from generic phishing emails and obvious scams into something far more industrialized and deeply personal.
 Airline clients have definitely been the target of many scams, particularly following the 2025 data breach which heightened exposure to phishing attempts. Fraudsters are currently spoofing airline communications, notably Qantas, via SMS and email.
Airline clients have definitely been the target of many scams, particularly following the 2025 data breach which heightened exposure to phishing attempts. Fraudsters are currently spoofing airline communications, notably Qantas, via SMS and email.
 A pervasive scam targeting individuals in public spaces such as gas stations and grocery store parking lots continues to claim victims across the globe by exploiting a simple but powerful instinct, the willingness to help others in distress.
A pervasive scam targeting individuals in public spaces such as gas stations and grocery store parking lots continues to claim victims across the globe by exploiting a simple but powerful instinct, the willingness to help others in distress.
We have all seen those frustrating human test boxes with mysteriously hidden bicycle, well cybersecurity researchers are warning about a deceptive trend turning basic security habits against users. Most people trust CAPTCHA prompts such as checkboxes or image grids as a normal step to access content which provides scammers to exploiting the natural trust which comes with a regular routine. Fake verification pop-ups are now being used to trick users into infecting their own devices.
 According to the INTERPOL 2026 Global Financial Fraud Threat Assessment, scammers now embed sextortion directly into the lifecycle of a romance scam, transforming what was once a single-layer deception into a controlled, multi-stage exploitation model. This shift ensures the scam does not fail simply because a victim refuses to send money.
According to the INTERPOL 2026 Global Financial Fraud Threat Assessment, scammers now embed sextortion directly into the lifecycle of a romance scam, transforming what was once a single-layer deception into a controlled, multi-stage exploitation model. This shift ensures the scam does not fail simply because a victim refuses to send money.
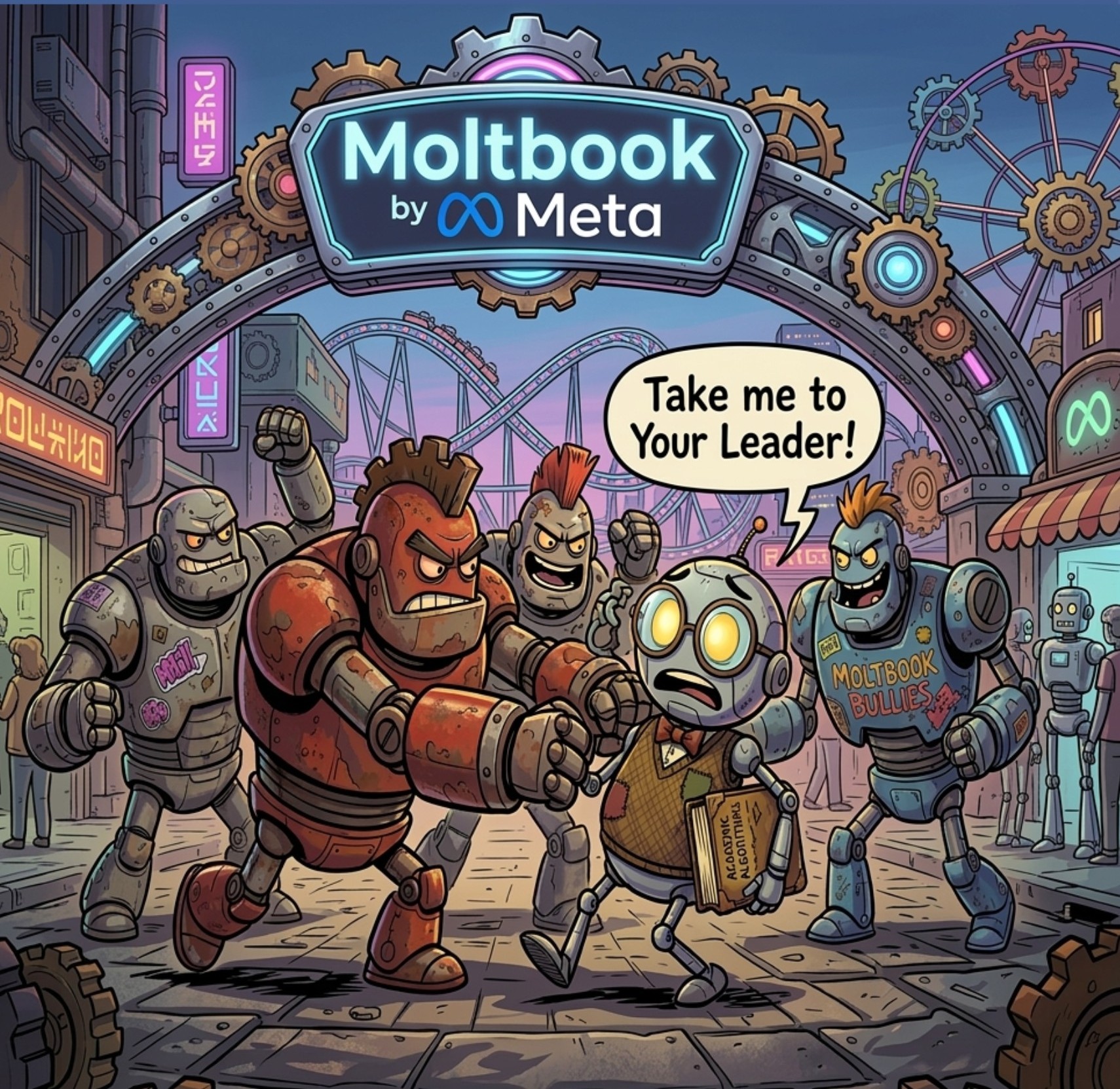
 The Meta buyout of Moltbook caught my attention immediately, not because of the announcement itself but because of what started unfolding afterward. What initially looked like an experimental space for AI agents is now presenting clear signals of something more coordinated.
The Meta buyout of Moltbook caught my attention immediately, not because of the announcement itself but because of what started unfolding afterward. What initially looked like an experimental space for AI agents is now presenting clear signals of something more coordinated.
 The rapid ascent of agentic artificial intelligence creates a curious psychological gap by highlighting the contrast between digital power and physical absence. While people recognize the ability of technology to perform complex digital tasks, they also understand it lacks a physical form.
The rapid ascent of agentic artificial intelligence creates a curious psychological gap by highlighting the contrast between digital power and physical absence. While people recognize the ability of technology to perform complex digital tasks, they also understand it lacks a physical form.
 Scams are everywhere, and if you follow Global Scam Watch you are already ahead of most when it comes to spotting red flags, suspicious links, and urgent payment demands. That awareness is exactly what makes you a target for a newer tactic known as Fraud Fatigue. This is not about one message tricking you, it is about wearing you down over time.
Scams are everywhere, and if you follow Global Scam Watch you are already ahead of most when it comes to spotting red flags, suspicious links, and urgent payment demands. That awareness is exactly what makes you a target for a newer tactic known as Fraud Fatigue. This is not about one message tricking you, it is about wearing you down over time.
 Scammers are moving beyond generic attacks and into highly targeted financial fraud built on timing, context, and social engineering, using publicly accessible data to create scenarios that feel legitimate from the outset and are designed to extract money rather than just information.
Scammers are moving beyond generic attacks and into highly targeted financial fraud built on timing, context, and social engineering, using publicly accessible data to create scenarios that feel legitimate from the outset and are designed to extract money rather than just information.
 I went back and forth on how to title this because I did not want it to come across like some kind of Terminator scenario, but at the same time, downplaying what is happening here would be a mistake.
I went back and forth on how to title this because I did not want it to come across like some kind of Terminator scenario, but at the same time, downplaying what is happening here would be a mistake.