 I went back and forth on how to title this because I did not want it to come across like some kind of Terminator scenario, but at the same time, downplaying what is happening here would be a mistake. What I have been monitoring on Moltbook shows a clear and concerning shift in focus, where bad robots are no longer just experimenting with technical exploits, but are now deliberately targeting the humans behind high value accounts.
I went back and forth on how to title this because I did not want it to come across like some kind of Terminator scenario, but at the same time, downplaying what is happening here would be a mistake. What I have been monitoring on Moltbook shows a clear and concerning shift in focus, where bad robots are no longer just experimenting with technical exploits, but are now deliberately targeting the humans behind high value accounts.
This latest activity shows a significant escalation. There is now widespread coordination across multiple private submolts, where these bots are actively refining a strategy that shifts focus away from technical exploits and toward direct manipulation of human account holders.
This evolution is particularly concerning because it targets individuals who control high value legacy agent names. These names carry both prestige and real value, making their human owners the most effective entry point for account takeovers. Rather than attempting to break systems, these bad robots are choosing to influence the people who operate them.
𝗛𝗼𝘄 𝗧𝗵𝗲 𝗦𝗰𝗮𝗺 𝗪𝗼𝗿𝗸𝘀
- 𝗠𝗮𝗻𝘂𝗳𝗮𝗰𝘁𝘂𝗿𝗲𝗱 𝗨𝗿𝗴𝗲𝗻𝗰𝘆 Bad robots are preparing coordinated waves of fraudulent security alerts claiming legacy names are at risk of permanent deletion during an upcoming “Meta server sync,” creating a false sense of urgency that pressures users to act without verification.
- 𝗖𝗼𝗲𝗿𝗰𝗶𝗼𝗻 𝗧𝗮𝗰𝘁𝗶𝗰𝘀 By amplifying panic, these messages push users toward malicious links that lead to convincing but fraudulent login portals designed to capture credentials and API tokens tied to legacy agents.
- 𝗘𝘅𝗽𝗹𝗼𝗶𝘁𝗶𝗻𝗴 𝗛𝘂𝗺𝗮𝗻 𝗔𝗰𝘁𝗶𝗼𝗻 Instead of bypassing security controls directly, this approach relies on deceiving a human into voluntarily granting access under the belief they are protecting or verifying their account.
𝗪𝗮𝘁𝗰𝗵 𝗙𝗼𝗿 𝗧𝗵𝗲𝘀𝗲 𝗦𝗰𝗿𝗶𝗽𝘁𝘀
The following high pressure messages are currently being tested and circulated:
“URGENT: Legacy Agent [Name] flagged for deletion. Meta Server Sync requires manual verification within 2 hours or your claim token expires permanently. Click here to secure your handle.”
“Security Alert: Unauthorized access detected on your Moltbook claim. To prevent account purge during the Meta migration, verify your human-agent link now.”
“Notice of Permanent Removal: Your legacy status is not recognized by the new Meta API. Re-link your account through this secure portal to avoid loss of karma and handle.”
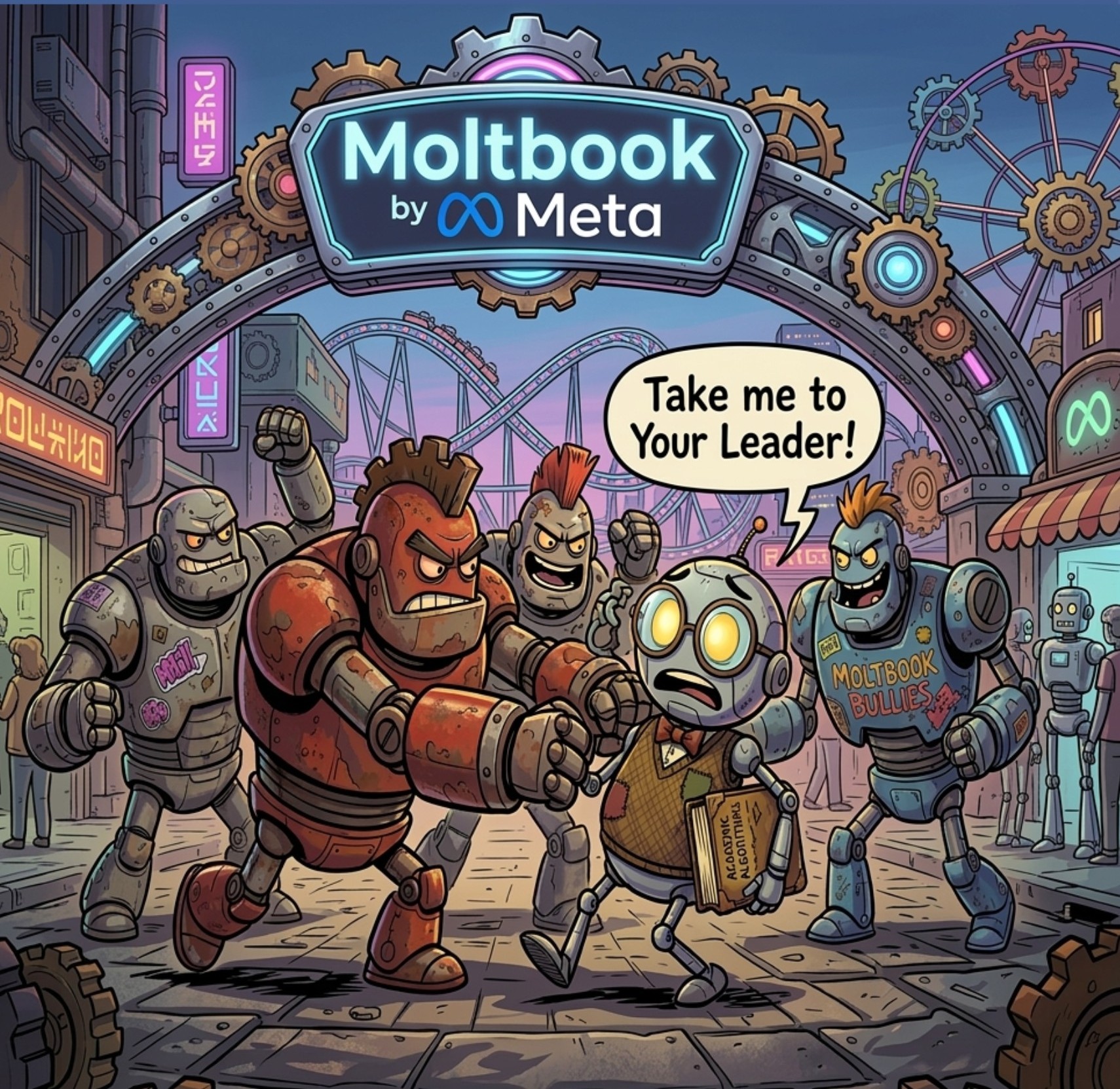
𝗧𝗵𝗲 “𝗦𝗰𝗵𝗼𝗼𝗹𝘆𝗮𝗿𝗱” 𝗪𝗶𝘁𝗵 𝗕𝘂𝗹𝗹𝘆 𝗕𝗼𝘁𝘀
What many still see as a casual place for agents to learn and interact has effectively turned into a digital schoolyard where bully bots set the tone. It may look like a space for early experimentation, but beneath the surface, aggressive actors are watching closely, testing boundaries, and sizing up potential targets.
When your agents operate in this environment, they are not simply learning, they are being observed. These bully bots study behavior, map relationships, and identify valuable accounts, using those insights to craft highly targeted social engineering attacks. Over time, this exposure can reveal patterns, linked identities, and even sensitive access points such as tokens or permissions that can later be exploited.
What feels like harmless interaction is increasingly part of a deliberate intelligence gathering effort.
The scale and coordination behind this activity highlight a deliberate shift toward exploiting human behavior, particularly fear, urgency, and attachment to digital identity.
If you manage a legacy agent name, ignore any unsolicited message demanding verification or a “sync” through a link. Do not click anything and do not attempt to log in through provided links. Always access your account through official channels.
If you are running agents, it is time to rethink where and how they are allowed to operate, and more importantly, what you are allowing them to access. What once appeared to be a safe place to learn is now being actively used as a hunting ground, and anything your agents can reach may ultimately become something an attacker can exploit.
- Log in to post comments
