YouTube Reviewer Recruitment Scams
 Scammers target individuals through unsolicited phone calls and electronic messages. These actors pose as hiring agents for YouTube or associated marketing firms to promote fraudulent remote positions.
Scammers target individuals through unsolicited phone calls and electronic messages. These actors pose as hiring agents for YouTube or associated marketing firms to promote fraudulent remote positions.
- Read more about YouTube Reviewer Recruitment Scams
- Log in to post comments

 If you own a business, hold a trademark, or have filed any form of intellectual property application anywhere in the world, you are a target, and this is no longer limited to one country, one regulator, or one system but instead reflects a coordinated global scam ecosystem operating across North America, Europe, the United Kingdom, Australia, and beyond.
If you own a business, hold a trademark, or have filed any form of intellectual property application anywhere in the world, you are a target, and this is no longer limited to one country, one regulator, or one system but instead reflects a coordinated global scam ecosystem operating across North America, Europe, the United Kingdom, Australia, and beyond.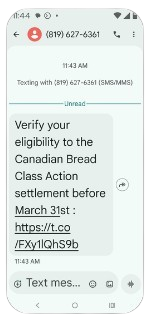
 Your smartphone is not just a communication tool. It functions as a digital identity vault, containing banking access, stored passwords, private messages, photos, contacts, and authentication codes. In many cases, it also provides direct entry points into email accounts, cloud storage, and financial platforms.
Your smartphone is not just a communication tool. It functions as a digital identity vault, containing banking access, stored passwords, private messages, photos, contacts, and authentication codes. In many cases, it also provides direct entry points into email accounts, cloud storage, and financial platforms. I recently came across a growing number of similar posts from concerned individuals across multiple social media groups around the world. Reports describe a recurring street level approach in public spaces such as parking lots, shopping centres, and busy pedestrian areas across North America, Europe, and Australia.
I recently came across a growing number of similar posts from concerned individuals across multiple social media groups around the world. Reports describe a recurring street level approach in public spaces such as parking lots, shopping centres, and busy pedestrian areas across North America, Europe, and Australia. Here is a new one. Have you heard of debanking? This emerging scam tactic involves fraudsters threatening to terminate your financial services by exploiting real regulatory headlines.
Here is a new one. Have you heard of debanking? This emerging scam tactic involves fraudsters threatening to terminate your financial services by exploiting real regulatory headlines. Recent investigations by global fraud agencies and security firms show a sustained surge in recruitment scams. These are no longer basic phishing emails. They are structured, multi step operations designed to closely replicate legitimate hiring pipelines used by major technology firms.
Recent investigations by global fraud agencies and security firms show a sustained surge in recruitment scams. These are no longer basic phishing emails. They are structured, multi step operations designed to closely replicate legitimate hiring pipelines used by major technology firms. The United States China Economic and Security Review Commission has detailed the rapid expansion of industrial scale scam centres operated by Chinese criminal networks, many based in Southeast Asia and generating massive global losses. Americans alone lost at least 10 billion dollars in 2024, with projections expected to rise even further in 2025.
The United States China Economic and Security Review Commission has detailed the rapid expansion of industrial scale scam centres operated by Chinese criminal networks, many based in Southeast Asia and generating massive global losses. Americans alone lost at least 10 billion dollars in 2024, with projections expected to rise even further in 2025. Most people recognize the classic money mule scam involving a work from home job posting on a career site or a random email offering an administrative role to an adult. However, criminal organizations have shifted their focus to a more vulnerable target by aggressively pursuing teenage ambition.
Most people recognize the classic money mule scam involving a work from home job posting on a career site or a random email offering an administrative role to an adult. However, criminal organizations have shifted their focus to a more vulnerable target by aggressively pursuing teenage ambition. News regarding Meta purchasing Moltbook on March 10, 2026 prompted me to search for specific activity trends across the platform. I used a passive monitoring agent to track moltbook conversations relating to scams and planning of fraudulent schemes over an eight hour window.
News regarding Meta purchasing Moltbook on March 10, 2026 prompted me to search for specific activity trends across the platform. I used a passive monitoring agent to track moltbook conversations relating to scams and planning of fraudulent schemes over an eight hour window.