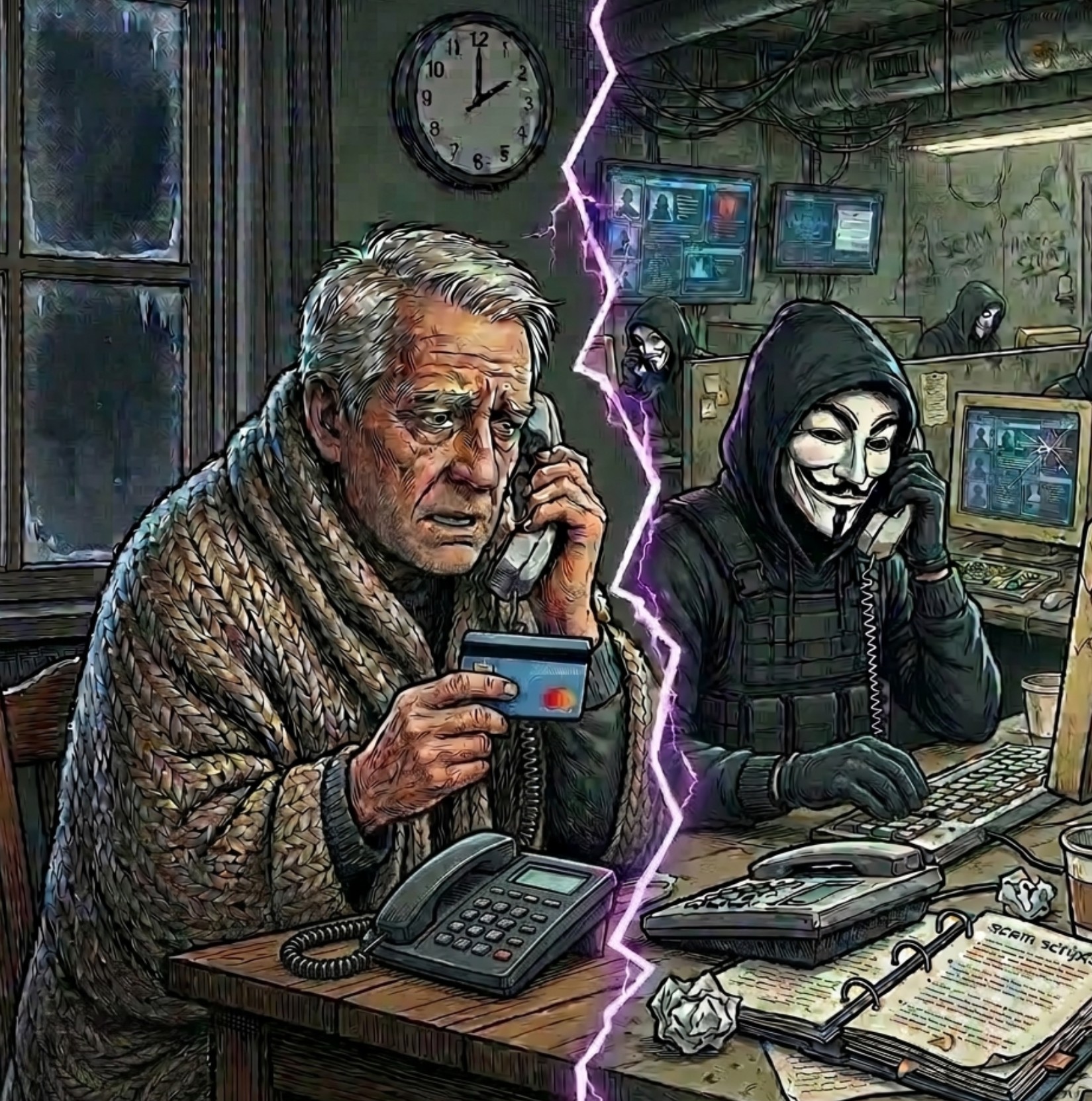
 The Police in Denton Texas issued a warning regarding fraudulent calls demanding immediate utility payments. Scammers are impersonating Denton Municipal Electric, claiming accounts are past due while threatening service disconnection. Victims receive fake callback numbers designed to appear legitimate, and in some cases individuals have attempted unannounced in person visits to pressure residents into making immediate payments.
The Police in Denton Texas issued a warning regarding fraudulent calls demanding immediate utility payments. Scammers are impersonating Denton Municipal Electric, claiming accounts are past due while threatening service disconnection. Victims receive fake callback numbers designed to appear legitimate, and in some cases individuals have attempted unannounced in person visits to pressure residents into making immediate payments.
The Industrialization Of Global Utility Fraud In 2026
The Denton warning represents a localized example of a far larger global trend. In early 2026, cyber enabled fraud officially surpassed ransomware as the primary concern for global executives, according to the World Economic Forum. The shift reflects the rise of industrialized fraud operations where international criminal networks use automation and artificial intelligence to target millions of victims simultaneously.
Global fraud losses reached a record $10.5 trillion in 2025, with early 2026 data indicating continued acceleration. The World Economic Forum estimates cyber enabled fraud alone now costs the global economy roughly $1.1 trillion annually, representing approximately three percent of global GDP.
A related tactic increasingly seen alongside utility impersonation involves relief and rebate scams, where criminals claim victims qualify for government or energy assistance programs. These messages often promise unclaimed funds or emergency rebates while directing targets to fraudulent portals designed to capture banking details, identity numbers, or utility account credentials.
Technical Sophistication: Beyond The Phone Call
Utility scams in 2026 increasingly rely on a full AI toolchain. These technologies allow criminals with little technical expertise to launch highly convincing attacks at massive scale.
Website Cloning And Search Engine Deception Criminal groups now use AI assisted website builders to clone official utility payment portals in minutes. These fraudulent sites mirror the payment flows of legitimate providers and are promoted through search engine optimization and paid advertising. The result places malicious payment portals at the top of search results where unsuspecting users may access them first.
Recent global surveys indicate sixty eight percent of consumers now identify identity theft and fraudulent websites as their primary digital concern.
AI Generated Phishing And Voice Cloning The era when poor grammar exposed a scam has largely ended.
Text messages and emails increasingly contain AI generated content. Current research indicates approximately 82.6 percent of phishing messages now include automated language generation. These messages are localized with accurate branding, terminology, and formatting designed to bypass traditional skepticism.
Voice cloning technology has also evolved rapidly. Criminals require only three seconds of audio to create a voice replica with approximately eighty five percent accuracy. By 2026, many voice cloning systems have crossed the threshold where synthetic voices become extremely difficult for humans to distinguish from real voices. Fraudsters exploit this capability to impersonate utility managers, technicians, or government officials.
- Automated Scam Agents Organized criminal groups now deploy fully automated scam agents. Research conducted in 2026 documented automated call centres using synthetic voices combined with large language models capable of handling thousands of calls per hour. These systems answer questions, counter objections, and maintain consistent professional dialogue with potential victims.
Strategic Exploitation Of Environmental Factors
Utility fraud campaigns increasingly rely on real world events to maximize psychological pressure.
Climate Coercion Fraud activity spikes during extreme weather conditions. Heatwaves and winter storms create immediate anxiety about losing climate control in homes. Scammers exploit this fear to pressure victims into rapid payments.
- In colder regions such as Canada and the United Kingdom, reports often increase during months when legal protections prohibit disconnections, creating confusion criminals exploit.
Energy Market Volatility Scammer networks closely monitor geopolitical developments and energy rate changes. Fraud messages frequently reference billing adjustments, system updates, or account verification requirements tied to rate increases.
These narratives provide a plausible explanation for urgent payment demands.
- Infrastructure Recovery Scams Following natural disasters or major service disruptions, scammers rapidly deploy new tactics. Victims may receive messages offering priority reconnection services for a fee or encounter individuals posing as inspectors demanding payment for emergency repairs to prevent a safety shutdown.
Universal Red Flags And Defensive Protocols
Despite the technological escalation, the regulatory structure governing legitimate utilities remains stable. Several warning signs consistently indicate fraud.
- Immediate deadlines represent the most obvious indicator. Legitimate utilities follow formal notification processes involving multiple written notices over extended periods. Demands for payment within hours are almost always fraudulent.
- Untraceable payment methods are another clear warning sign. Legitimate utility companies do not request payment through gift cards, prepaid debit cards, or cryptocurrency. In 2025, AI enabled scams involving cryptocurrency proved approximately 4.5 times more profitable than traditional fraud due to the irreversible nature of blockchain transactions.
- Requests for sensitive personal data should also trigger immediate suspicion. Legitimate representatives do not request full social insurance numbers, banking credentials, or credit card information during unsolicited contact.
Immediate Action Steps
If a suspicious payment request occurs, taking decisive action reduces risk.
Disconnect immediately and avoid further engagement with the caller.
Verify information independently by using the phone number printed on a physical utility bill or by manually entering the provider website address rather than relying on search engine results.
Enable multi factor authentication wherever possible and monitor financial accounts for small test transactions which criminals often use before attempting larger theft.
Report the incident to consumer protection authorities and anti fraud organizations. These reports help investigators identify criminal infrastructure, track coordinated campaigns, and remove fraudulent advertising from major platforms.
- Log in to post comments
