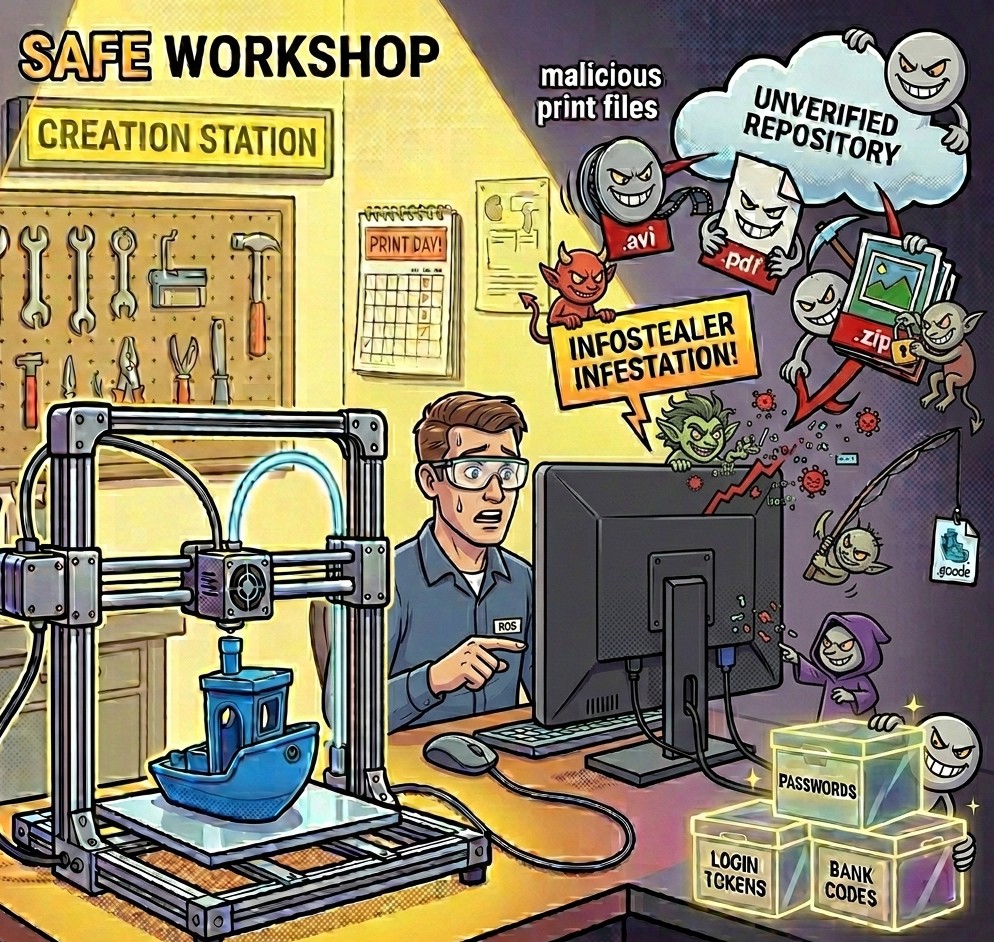
 The 3D printing community relies on a culture of open sharing. Whether seeking a replacement part or a complex artistic model, users frequently download files from various repositories and forums. However, opportunistic criminals now exploit this trust by turning seemingly harmless hobbyist files into delivery vehicles for malicious software. Recent reports highlight a disturbing trend where users download print files only to find their systems infected with persistent malware designed to harvest every saved password and session token.
The 3D printing community relies on a culture of open sharing. Whether seeking a replacement part or a complex artistic model, users frequently download files from various repositories and forums. However, opportunistic criminals now exploit this trust by turning seemingly harmless hobbyist files into delivery vehicles for malicious software. Recent reports highlight a disturbing trend where users download print files only to find their systems infected with persistent malware designed to harvest every saved password and session token.
The Mechanics of the 3D Print Scam
While a standard 3D model file like an .stl or .obj is typically inert data, the danger resides in how these files are bundled and delivered. Bad actors often utilize search engine optimization poisoning to push malicious sites to the top of search results or upload "premium" models to popular repositories.
The infection usually occurs through three primary methods:
- Malicious G-code: Unlike raw models, G-code contains direct instructions for a printer. These individuals embed scripts within these files exploiting vulnerabilities in slicing software or networked printer firmware.
- Executable Wrappers: Many downloads arrive as compressed archives. These folders often contain a small executable or script disguised as a "readme" or "configuration" file. Opening these files deploys an "infostealer" targeting browser data immediately.
- Slicer Software Exploits: Outdated slicing programs may have security flaws. A specially crafted model file can trigger a buffer overflow, allowing the malicious code to execute the moment a user imports the model.
Expanding the Attack Surface: From MatrixPDF to Media
The strategy of weaponizing familiar files follows the pattern established by toolkits like MatrixPDF. In that scenario, criminals disguise harmful threats as trusted documents by embedding deceptive prompts claiming to unlock or secure the file. This same illusion of legitimacy is now applied to images and video files.
Image Files and Steganography
Steganography involves hiding malicious code within the actual pixels of an image. A .jpg or .png file appears perfectly normal to the naked eye, yet it contains encrypted binary data. If a user has already been compromised by a small starter script, the script extracts the hidden code from the image and assembles the virus directly in the system memory.
Video Files
While the video data itself is rarely the virus, the software used to play it can be a target. Attackers create files using less common formats designed to exploit vulnerabilities in unpatched media players. When the software fails to parse the corrupted data, it creates an opening for arbitrary code execution.
The Persistence Problem
A hallmark of modern infostealers is their ability to remain on a system after discovery. Victims often report the malware "regenerates" even after attempts to delete it. This persistence is achieved by burying the virus in the Windows Registry, creating recurring tasks in the Task Scheduler, or hiding within system folders. A simple "Reset this PC" often fails to remove these deep-seated hooks, necessitating a complete drive format and a clean operating system installation.
How to Protect Yourself
Maintaining safety requires a shift in how we handle downloaded content. Maintaining awareness and exercising critical thinking remain the strongest defences against these threats.
- Prioritize Raw Data: Stick to geometric formats like .stl or .step. Never run pre-sliced G-code from unverified sources.
- Keep Software Updated: Ensure your operating system and all media players are up to date to minimize vulnerabilities.
- Disable JavaScript: As noted with the MatrixPDF threat, disabling JavaScript in PDF readers prevents hidden code from running.
- Use Sandbox Environments: Open experimental or unverified files inside a virtual machine to isolate potential threats from your primary data.
If you suspect an infection has occurred, treat every account as breached. Change your passwords using a different, clean device and implement multi-factor authentication across all platforms.
- Log in to post comments
